7 Answers Ransomware Victims Need to Know
Click on each of the commonly asked questions below to see answers.
1. How do I recover from a ransomware attack?
Ransomware attacks are becoming increasingly common, and whether you are a small, medium, or large company, you are a target.
If you have been an unfortunate victim of a ransomware attack, you are likely overwhelmed and wondering what the next steps are. We have been involved in many recovery efforts and have outlined what our clients experience as the most common and important steps when recovering from a ransomware attack.
The process will be lengthy, expensive, and stressful but putting together a well-rounded recovery and response team will be invaluable. In the initial stages, engage a lawyer and find out what insurance covers. Have your response team assess the current situation (identify type of ransomware and damages) and start collecting forensic data. Decide if you will pay the ransom and/or if you will hire a negotiator that specializes in ransomware. Keep the attack confidential while you lay out your plan…continue to review the plan with your team…and then execute with vigor. You will then need to develop and implement a cybersecurity strategy moving forward and make this a consistent part of your overall business strategy. To read a more detailed explanation of the steps, click HERE.
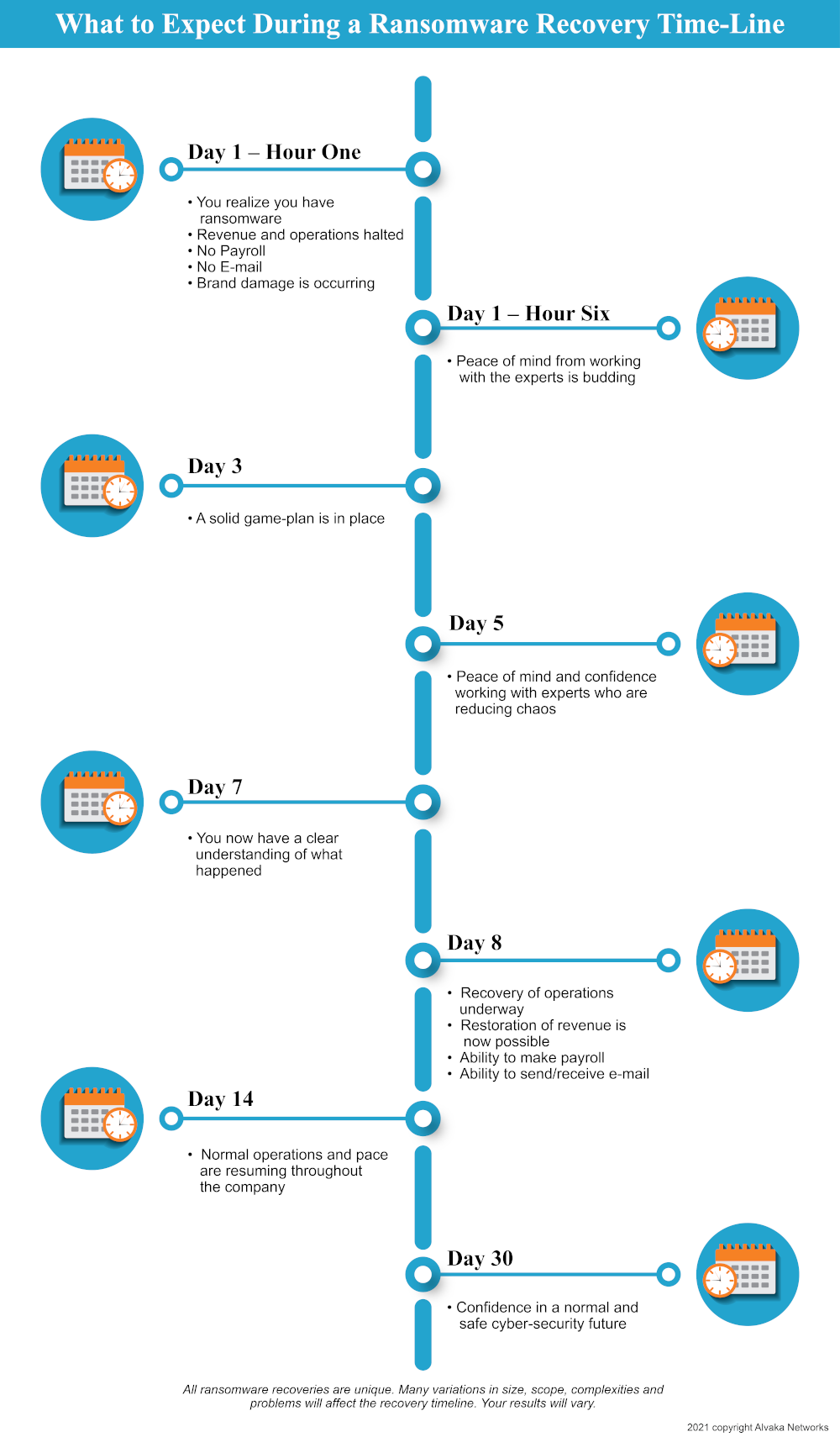
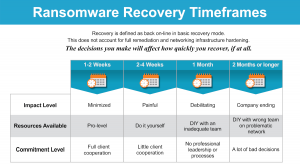
2. How long does it take to recover from a ransomware attack?
The time it takes to recover from a ransomware attack can vary widely. For most companies who are unprepared and unexperienced, recovery efforts will typically fall between the two to four week mark. However, recovery time can be cut in half (about one to two weeks) if you have a well-managed effort and experienced team.
Prolonged recovery efforts are a result of many factors, and often come at the expense of the company’s bottom line and reputation. In some cases, the company may never recover. It is therefore crucial to consider all of the variables that can impact the time it takes to recover from an attack. Below are five variables we find to have the most influence.
1. The most important is having a well-coordinated and experienced team of experts (includes ransomware recovery team, insurance company, incident response team, lawyers, ransomware negotiator, etc.)
2. Type of ransomware and the experience level of the attackers.
3. Size of your IT infrastructure.
4. Configuration of your It infrastructure before the attack.
5. The experience level, maturity, and size of your IT team.
If you would like to read the full blog, click HERE.
3. How much will it cost to recover from a ransomware attack?
If your company has been hit with ransomware, you might be wondering how much the incident will cost you. There are many variables that will determine your costs, including company size, the complexity of your network and applications, and which ransomware you have been infected with. There are two cost categories to consider: Cost to Recover and Total Cost of Ransomware Recovery (TCRR).
The Cost to Recover includes the amount of cash you will need to pay out for recovery activities like incident response, decryption and system recovery, forensics, and the ransom amount paid (if any). The Total Cost of Ransomware Recovery (TCRR) will also include the lost revenue associated with the incident, due to downtime, brand reputation, etc. Your downtime will vary depending on the specifics of your attack.
We have created a Ransomware Recovery Cost Calculator that will help you determine your estimated TCRR.
4. If I pay the ransomware demand, will I get my data back?
With any ransomware incident, you are dealing with criminals who will not hesitate to harm you further to receive payment out of you.
Additionally, the odds aren’t in your favor if your backups are outdated – like most ransomware victims. So, you are wondering, should I trust the word of these cybercriminals? No, you shouldn’t. However, these threat actors have a reputation they must maintain. If the cybercriminal industry is known for having individuals that don’t provide a decryption key when paid, well, then their leverage factor gets significantly reduced. No one would pay a ransom knowing that the most likely scenario will be they get scammed. These cybercriminals are making too much money, and they wouldn’t risk ruining that. Now, that doesn’t mean there have been zero instances where a cybercriminal didn’t provide a decryption key. Therefore, if you decide to pay a ransom, we recommend Coveware for the negotiation process.
If you would like to read the full blog, click HERE.
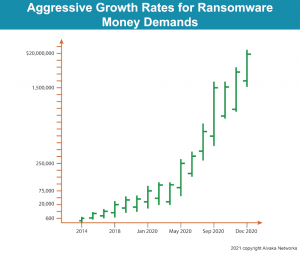
5. How much is the average ransomware demand?
Each ransom attack can vary significantly, so it quite difficult to pinpoint the exact amount of a typically demanded in ransomware cases. However, history shows a clear trend – an increasing ransom amount. In the early years, a $200M per year company would only expect a ransom of a few hundred dollars.
By 2018, threat actors became more efficient and created in-depth plans, allowing them to price a ransom proportionally with a company’s size. In 2020, a typical ransom for a company producing $20M annually would receive a ransom amount of $50-100k. By the end of the year, ransoms were pushing themselves into the millions, and in November, we saw our first $20M ransom.
Overall, the ransom amount depends on many factors, like what tools the threat actors are using, number of servers, number of files, total storage, and more. Additionally, according to a report by Coveware, ransom payments are increasing (see Ransomware will likely get worse in 2021), and findings show that the typical ransom amount has risen 31% to $233,817, as of late 2020.
If you would like to read a detailed explanation regarding this subject, click HERE.
6. Who are the best ransomware recovery service companies?
Alvaka Networks has been involved in many recovery efforts and have first-hand experience working with companies that offer specific services when it comes to recovering from ransomware. The ransomware recovery process is complex and will require building a response team specific to your ransomware incident in order to be successful in your efforts.
Ransomware recovery service companies fall into three primary categories:
- Ransomware negotiation/decryption
- Incident response/containment
- Ransomware recovery/IT system rebuilding and recovery
It is unlikely you will find one ransomware recovery service company that offers the full stack of recovery services you need, so you will need to determine what you need and choose accordingly. Here are our recommendations for the Best Ransomware Recovery Services Companies.
7. Should I engage a lawyer after a cyber attack? Who are the best ransomware lawyers and cyber breach coaches?
Another crucial addition to your ransomware recovery response team should include a ransomware or cyber breach lawyer, usually specializing in ransomware, data exfiltration and phishing related business email compromise. They will be your trusted advisor throughout your ransomware and cyber breach recovery journey. A ransomware attack does not just cause a dire technical and business issue, but in many cases it can be a legal issue as well.
A ransomware and cyber breach lawyer will:
- engage and manage all parties involved in the recovery process
- provide important legal protections via attorney client privilege
- ensure compliance with the law
- help minimize and manage aftermath of a data compromise
- and much more
Based on our experience, we have provided a list of recommendations for the Best Ransomware and Cyber Breach Lawyers.
Additional Questions…
Which ransomware did I get infected with?
Each year, more sophisticated and harder-to-detect ransomware variants are developed and deployed onto unsuspecting companies. Having access to valuable and reliable ransomware resources and information can make all the difference.
When you’ve become a victim of ransomware, the crucial first step to recovery is to identify which variant the threat actors used. From there, the experience and knowledge of a professional ransomware removal team can be very beneficial.
There are many free, easy, and reliable ways to identify which ransomware variant has infected you. Once identification of the ransomware variant is successful, the recovery process via the deployment of an effective plan can begin. The specifics of each incident and what they require will vary from case to case, but you can generally expect common essential steps in a recovery effort.
If you would like to read a more detailed list, click HERE.
How do I prepare in advance to reduce the risk of ransomware and other cyber attacks?
As a network security provider, we have seen first-hand what the long and painful road to ransomware recovery can involve. The recovery process can take months and carry significant costs beyond insurance coverage and ransom demand. Fortunately, you can take steps to reduce your chances of becoming a victim.
Implement the below actions to reduce the risk of ransomware and other cyber attacks:
• Require multi-factor authentication
• Patch ALL systems frequently
• Manage or Remove Deprecated or End-Of-Life systems
• Update Firewalls and other firmware
• Enable strong spam (email) filters
• Implement user training and simulated attacks
• Filter network traffic
• Implement URL reputation services
• Limit access to data and other assets. Segment your network!
• Restrict remote systems access
• Use active scan antivirus/antimalware
• Remove all local admin rights and restrict non-IT staff rights
• If you can, BLOCK (and if not, Disable) Office macros
• Implement a backup system that covers all critical data and system states. Isolate backups from the network; institute insider protections; store offline image templates, license keys, source code and copies of executables
• Get breach insurance that covers ransomware
• Ensure your exception-based monitoring can immediately trigger alerts
• Create a Business Continuity Plan (BCP) for security events
This is a crucial topic. Please click HERE to read the more detailed explanation of these recommendations and what NOT to do.
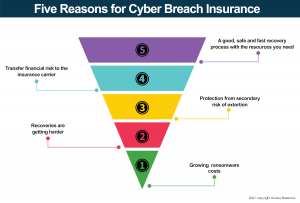
Should I Buy Cyber Breach Insurance? And Why?
Cyber breach insurance has grown to be a valuable asset over the last few years due to constantly changing trends in cybersecurity and threat actor tactics. So, should you invest in cyber breach insurance in 2021? Yes, and we’ll list out the top 5 reasons why you should.
1. The trends are against you. Each year, threat actors become more efficient and smarter in proportionally pricing a ransom to your company’s size. In the early years, a typical ransom would have cost only a few hundred dollars, but now threat actors can accurately estimate your revenue and price accordingly.
2. Unfortunately, it is harder to recover from ransomware than before. In 2018, a nasty habit among threat actors developed – deletion of backups. Now, you can expect cybercriminals to learn everything about your network, attack with a plan, delete backups, and encrypt all your data.
3. Not only will they delete and encrypt files, but they will also attempt to extort you by threatening to sell your confidential information.
4. This one is obvious. The transfer of risk to the insurance carrier. Also, ensure your cyber breach insurance covers the ransom, forensic, ransom negotiation, legal representation, ransomware recovery, public relations, fines and breach notification, and business interruption.
5. Following a sound ransomware recovery process with adequate resources is key.
If you would like to read a more detailed list, click HERE.
How much cyber breach insurance do I need?
When it comes to cybersecurity threats and the potential losses, business decision makers might be wondering just how much cyber breach insurance coverage they need. A simple answer to this, given averages and trends, is that your coverage should range from at least $1,000,000 to $5,000,000. Additionally, you will want to make sure your total limit is around 10% to 20% of your annual revenue to cover business interruption losses.
A more analytical process to determine what your coverage should be is to estimate how much a cyber incident, like ransomware, is likely to cost you if your company were attacked. Getting hit with ransomware is certainly not the only reason you would need cyber breach coverage, however, we recommend using a ransomware breach as the best indicator for how much coverage you should buy due to the following…
- Ransomware is the most prevalent cyber breach incident, with significant cost implications
- Ransomware attacks commonly include an extortion demand, with bad actors threatening to release data that was exfiltrated from the victims’ network
- Ransomware attack cost components include every expense category involved in a cyber breach event, including legal counsel, incident response, digital forensics, ransom negotiation, and more
To estimate your cost of a ransomware attack, you can use our Ransomware Recovery Cost Calculator below. The calculator calculates in real time and we encourage you to play with some differing values in some “what if” type situations.
Click HERE to read more about what you should be looking for in a cyber breach insurance policy, including a Q&A with an expert insurance broker.